71-75 Shelton Street. Covent Garden.
London WC2H 9JQ. United Kingdom
Find us here
71-75 Shelton Street. Covent Garden.
London WC2H 9JQ. United Kingdom
71-75 Shelton Street. Covent Garden.
London WC2H 9JQ. United Kingdom
71-75 Shelton Street. Covent Garden.
London WC2H 9JQ. United Kingdom
You will love all of the features in OBMeet with 100% guaranteed satisfaction.
Start your video webinar in minutes. Quickly turn conference rooms into collaboration centers with OBMeet.
Get StartedContent creators can start video conference, chat and stream live to Facebook, Youtube, Twitch and more.
Get StartedStart a conversation and authoritative presence, chat and stream live to Facebook, Youtube, Twitch and more.
Get StartedReduce the cost for education and collaborate with schools to boost performance.
Get StartedLearn to speak a language with confidence or work conveniently with us from anywhere.
Get Started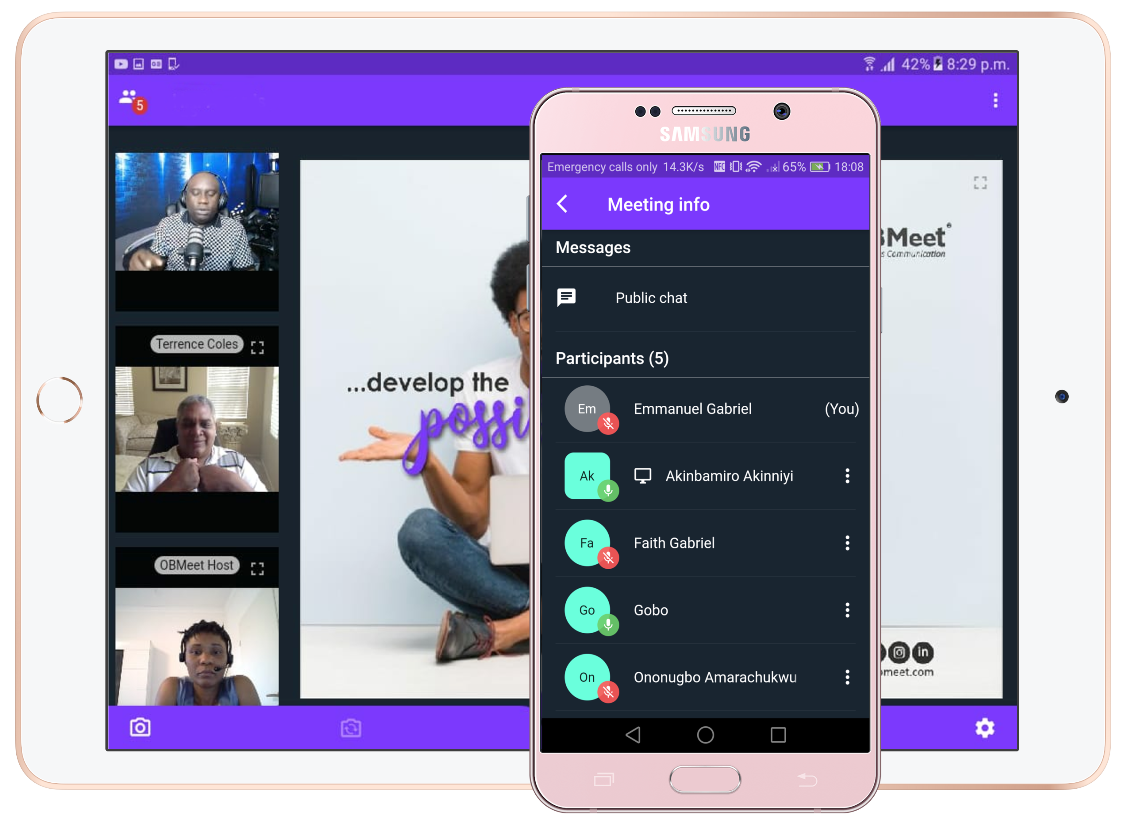
OBMeet® video conference allows everyone to hold video or conference meeting with more than 250 participants per room. Participants can capture and record video.
* Bring HD video to your meetings with support for up to video participants on screen.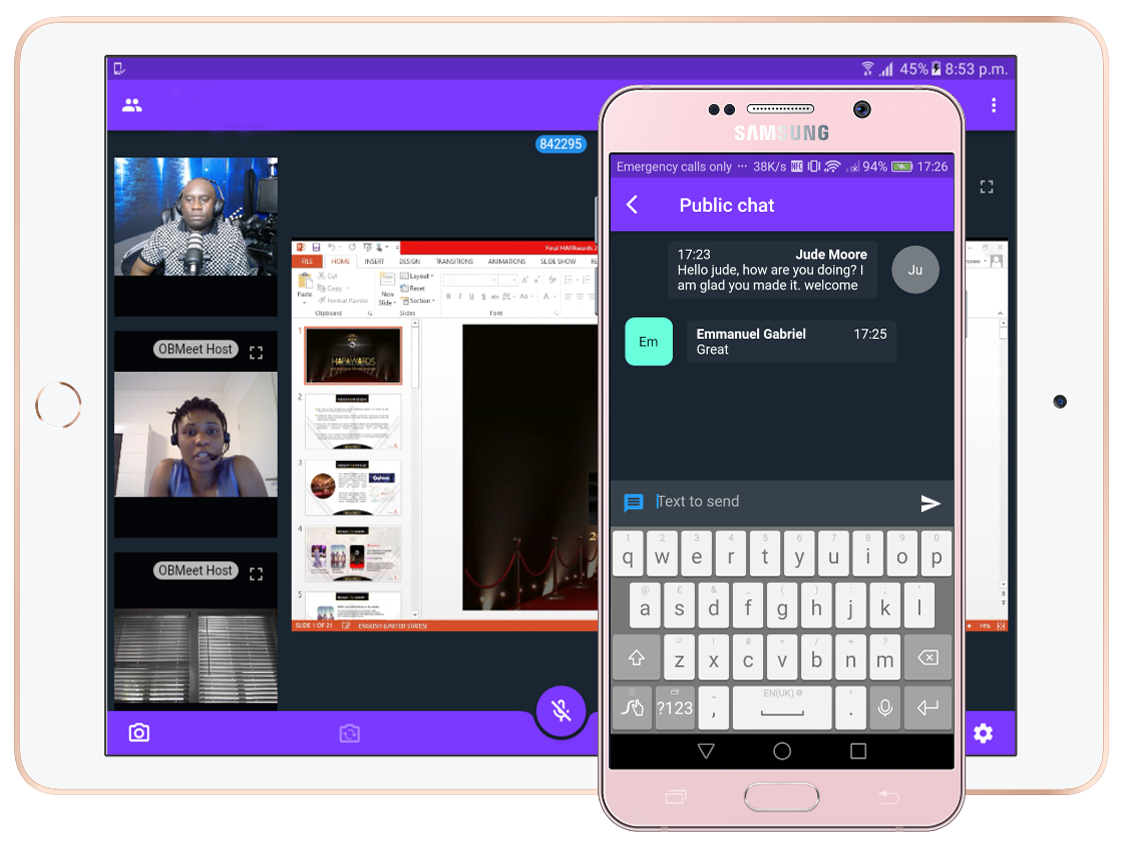
OBMeet allows you to chat and screen share your computer screen. Other users are then able to see your screen and watch your activity in real-time - ideal for scenarios such as online presentations or meetings.
* Screen sharing spares you the time and effort of having to send files, documents, or videos.
